Our platform has been designed from the beginning to provide flexibility and reduce the maintenance efforts of your payment operation.
Through our single integration, a microservices architecture composed of platform components and an abstracted and standardized means of processing transactions, we allow you to decouple your payments infrastructure. This grants you the opportunity to expand globally without struggles or delays.
- 1
Avoid the development and maintenance of custom connections to payment stakeholders like acquirers, PSPs, gateways, processors, and fraud vendors.
- 2
Avoid building your own payment applications.
- 3
Reduce your PCI DSS scope, by keeping sensitive data off your servers while maintaining a seamless checkout experience across every channel.
Platform Components
Learn more about our infrastructure and microservices. Understand how the the Switch Platform components can better aid with your payments operations.
Platform Components is all about seeing the big picture.
Core Concepts
Core Concepts lays the foundations for grasping how we process any payment method through any provider whilst only requiring a single integration flow.
Core Concepts is all about getting on the same page.
Security
It takes a lot of effort to make sure payments are secure. Get to know our security principles and how we enforce them.
Platform Components
The Switch payments Platform enables real-time transactions on an any-to-any basis: multi-channel, multi-network, multi-method and multi-currency. This abstraction feeds a shared, event-based database on top of which run multiple internal applications and external value added services. These make up our Platform Components.
The Switch Platform is composed of several cloud-agnostic micro services that can be deployed independently on cloud or on-premise security-certified servers. Microservices include Processing, Dynamic Routing, Reconciliation, Risk, Analytics, Dashboard, Merchant, Reporting, Event-Sourcing, Auth, Load-Balancers, Service Discovery, Monitoring, Logging and Security Services.
- 1
Complete Control
Switch's infrastructure provisioning and deployment is fully automated, enabling horizontal scalability, zero-downtime deployments, fault-tolerance and disaster recovery.
- 2
Complete Security
The Switch Platform is also PCI level 1 certified and follows the strictest industry security standards.
The Switch Platform is completely modular, and each Platform Component can consume both internal services or third party’s. This system architecture allows for maximum flexibility on custom setups.
- 1
The Switch single integration flow can support custom transaction collection parameterisation without any changes in your code for multiple payment channels.
- 2
The Switch Platform feeds its own and 3rd party’s Dashboard through REST APIs.
- 3
All Processing integrations, both international card schemes and any alternative payment methods, can be added in the transaction flow without any changes to your code
Processing
The Switch Processing application uses the same abstractions for all transactions, regardless of them being synchronous or asynchronous, payins, payouts or marketplaces, redirection-based, pre-payments or post-payments, one-time or recurring. This way, you are able to add new payment channels without any changes in your code, while keeping your checkout experience fully customisable.
Future Proof
Our client-side library will check all payment channels enabled on any specific merchant account, returning a form schema for each of them. A form schema is a description of all the payment data fields required to process a specific payment method. It will then be possible to dynamically build any form based on that list. This means that if more payment channels are added in the future, the existing code will be ready for them.
Single Integration
The single integration can adapt to any transaction flow, such as specific data collection, custom payment configurations, technical requirements and UX specifications.
Tailor Made
The abstraction created on our backend to support the multitude of payment flows can also enable authorization for custom setups. These can include not only financial transactions such as POS and private label schemes, but also virtual value such as loyalty and coupons, making Switch one the most comprehensive and flexible payments platforms available on the market.
Dynamic Routing
Our Dynamic Routing component provides real-time switching capabilities which allow us to select the best provider for a given transaction.
Industry Cognizant
Besides enabling connections industry-wide, Switch adds a rules-based layer that intelligently routes transactions between a wide network of payment channels in real-time to maximize payments performance.
Flexible
A transaction profiling system is processed to set default transaction metadata, which is used to define custom rules for automatic switching in real time at transaction level.
Reconciliation
Reconciliation of incoming settlements against bank accounts is a complex process. This activity becomes even more challenging when a business relies upon multiple providers, with multiple reporting structures. Reconciliation helps oversee and uniformize transaction data towards thoughtful monitoring of your payment operations.
Source Standardization
The Switch Reconciliation engine processes transaction statements from different sources and formats into a single data structure.
Time Saving
Reconciliation produces settlement events that automate and simplify the monitoring process.
Risk
Fraud management tools perform differently based on specific business verticals and require trained models with high switching costs. This makes their integration to new providers a costly and time-consuming endeavour. Too often, fraud defense also comes at the cost of conversion rates. Switch makes extensive use of data to maintain the perfect balance between fighting fraud, keeping shopper friction to a minimum and switching processes as simple as they get.
Thorough
A set of default transaction metadata is defined and communicated through risk events in real time. These events can be used to define custom Risk rules and output actions such as dynamic 3DS, review or transaction blocking.
Simple
As for any other platform component, Switch offers a modular approach to fraud management, supporting multiple third party security vendors in a single workflow.
Analytics
Switch uses Big Data technologies to capture, store, analyze, search, share and visualize voluminous and complex payment datasets. Our Platform transforms raw data into consumable information, generating valuable insights that empower payment managers to make better decisions.
Instantaneous Feedback
Every transaction parameter is indexed in the Switch lifecycle database and becomes readily available for processing through the Analytics API.
Diversity of Insights
You are able to perform queries to the database using multiple parameters to get operations insights, monitor your processing commissions or control bookkeeping.
Vault
In the payments industry, tokenization is the act of pseudonymization any sensitive information for secure storage and later use. The Switch Vault allows for the tokenization of any Switch parameter, this means it is even possible to use it in the creation of instruments for different charge types.
Added Security
By using Tokenization, you place another obstacle between your business and fraudsters. It is not possible to link tokens to the respective payment information and make use of stolen payment `instruments`.
One Click Payments
Tokenization allows customers to save their payment details in a secure manner, so that the next time they make a purchase they do not need to re-enter their payment data.
Core Concepts
Digital payments have been growing at a fast pace to support the ever evolving global commerce market. New means of payment, new regions, new regulation, new security guidelines, and new customer segments ensure the payments landscape is constantly shifting.
Adjusting to these new realities can be challenging and complex. Switch is here to simplify the process and put an end to the growing pains that come with expanding your business. Our platform was designed with flexibility in mind to support the growth of your payment operation. In order to achieve this, we defined core concepts in our architecture from the outset. These allowed us to maintain a single integration, no matter the payment method being processed, whilst giving you access to multiple Platform Components.
Single Integration Flow
First time's the charm. With Switch you get access to every present and future payment method, as well as all the tools required to run a professional and comprehensive payments operation through a single integration.
Providers
In the Switch Platform, a provider is a payments’ value chain stakeholder to which the Switch Processing application is connected to. Here are some examples of the providers we work with.
Acquirers
An acquiring bank, also known simply as an acquirer, is a bank or financial institution that processes credit or debit card payments on behalf of a merchant. The acquirer allows merchants to accept credit card payments from the card-issuing banks within an association.
Examples: Sberbank, Worldpay, JP Morgan.Acquirer Processors
Acquirer processors connect directly with merchants, card networks, and the acquirer, to exchange transaction information between all stakeholders. They provide the technical capabilities to communicate authorization and settlement messages between the acquirer and the card networks.
Acquirer processors handle the technical side of the acquiring business, they do not assume financial liability for the process, as they are not involved in fund management. This liability and risks lie on acquirers. Nonetheless, it is important to note that In some cases, the acquiring bank and acquirer processor are a single entity (e.g. Adyen, Elavon).
Examples: Redsys, Monext, SIBS.Payment Service Providers (PSPs)
A payment service provider (PSP) is a payment institution with the right to manage third party funds. It offers merchants multiple payment methods, namely credit card, direct debit, and bank transfers.
Typically, a PSP can connect to multiple acquiring banks, card networks, and payment networks, which makes the merchant less dependent on financial institutions by eliminating the burden of establishing these interactions directly. This can be especially relevant when operating internationally.
Examples: Stripe, Adyen, Mollie.Gateways
A payment gateway represents a technical layer that collects payment instrument credentials in the client-side and securely forwards them to the relevant payment service provider (PSP) or acquirer. The majority of gateway companies also offer other services.
Examples: Switch, PAY.ON, Braintree.Fraud Vendors
Fraud vendors are capable of predicting user intent and preventing fraudulent activity in real-time. They fundamentally manage risk and hinder financial crime.
Examples: Feedzai, Forter, Riskified.Tokenization Service providers
These institutions tokenize card data, which is the pseudonymization of credit cards sensitive data to facilitate compliance for merchants, PSPs, and acquirers. Tokenization service providers exist to grant a secure environment in which to store the card data sent by merchants.
Examples: Tokenex, VGS.Want to know more about Dynamic Routing?
Our Dynamic Routing component provides real-time switching capabilities which allow us to select the best provider for a given transaction.
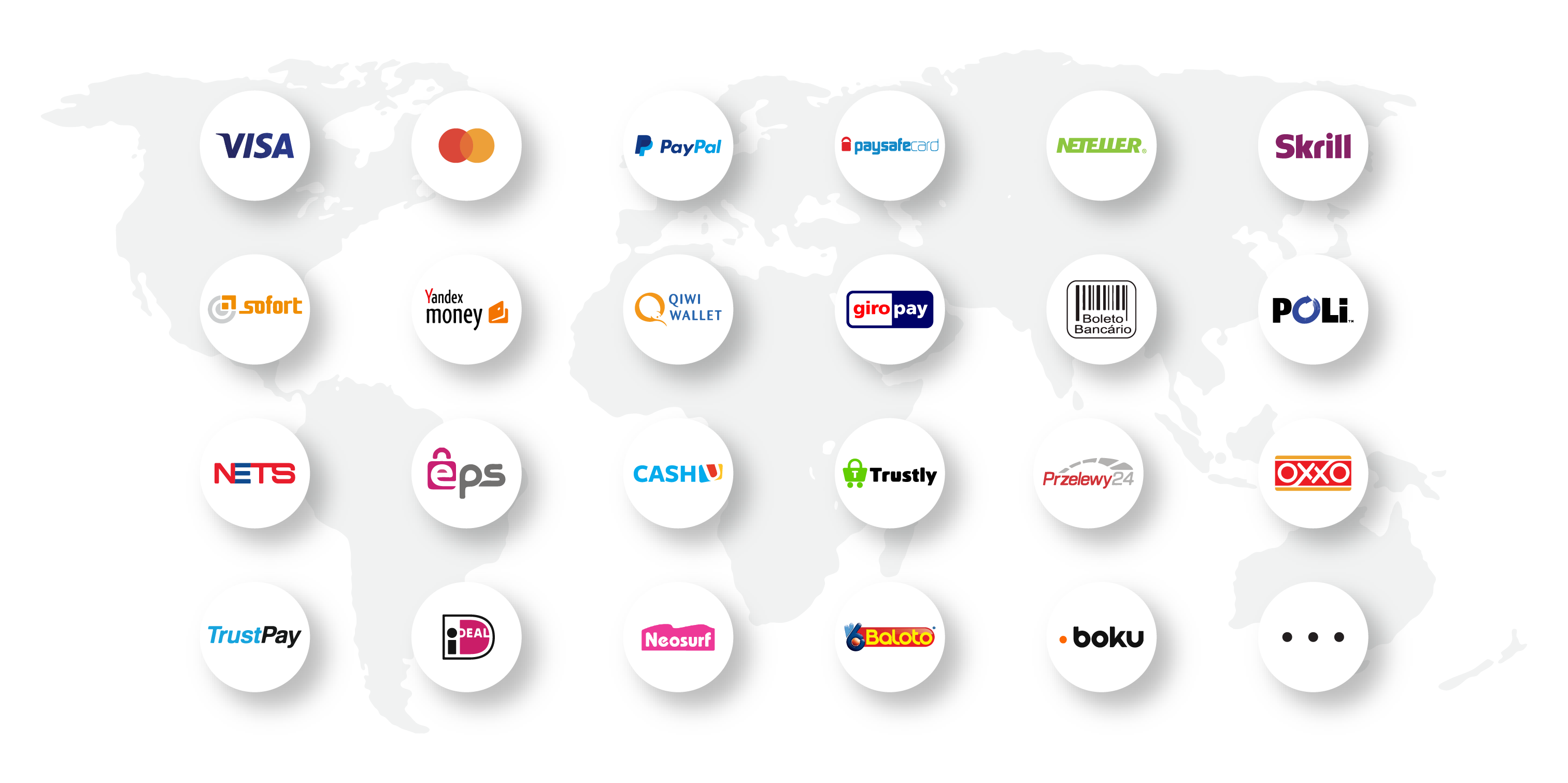
Payment Methods
In its broader definition, a payment method is any set of infrastructure and regulation that supports value exchange between a network of participants.
Cards are not the only way to pay for online transactions. Between bank transfers, direct debits, eWallets, mobile payments, local card schemes, pre-pay, post-pay and e-invoices, there are over 200 different types of alternative payment methods.
Alternative Payment Methods (APMs)
The designation of alternative payment method applies to any form of payment that is not cash or a card issued by a major bank. APMs are commonly used and increasingly adopted across sectors and territories to respond to consumer's trends. Accessing them is essential to any business.
Examples: Alipay, MBWAY, Bitcon.What about custom payment methods?
Created specifically to suit your needs, these custom payment methods have bespoke processing flows.
Get in touch with our Sales Department to know more.
Our platform allows you to process transactions using any payment method, from traditional credit/debit cards to alternative payment methods or custom payment methods like private label, credit-to-consumer, and loyalty schemes.
In the complex and diverse world of payments, there are multiple payment methods available in multiple markets.
Card
Physical or digital card issued by a financial entity that can be used for purchases. There are different types of cards available in the market, including debit, credit, and prepaid cards.
Examples: Visa, Mastercard, American Express, Union Pay, JCB.Bank Transfer
Electronic payment that is directly performed from one bank account to another. Can be done between two individuals or an individual and an entity.
Examples: SEPA, ACH, SWIFT.Pre payment
customers are required to buy and add funds to a card or voucher before starting a transaction, which means that these are usually authorised immediately.
Examples: SEPA, ELV (Elektronisches Lastschriftverfahren Germany), Bacs Direct Debit.Cryptocurrency
Digital asset designed to work as a medium of exchange wherein individual coin ownership records are stored in a digital ledger or computerized database using strong cryptography to secure transaction record entries, to control the creation of additional digital coin records, and to verify the transfer of coin ownership.
Examples: Bitcoin, Ethereum, Litecoin.Carrier Billing
Online payment method that allows customers to use their phone carrier bill to pay mostly for digital goods.
Examples: Boku, Dao Pay, Fortumo.e-Wallet
Digital wallet that can store funds and perform electronic payments. It can be connected to a bank account and used to store card details.
Examples: PayPal, Neteller, Skrill, Alipay, WeChat Pay, V.me by Visa, Qiwi.Direct Debit
Gives banking customers the ability to authorize third-party creditors to debit funds from their checking account.
Examples: SEPA, ELV (Elektronisches Lastschriftverfahren Germany), Bacs Direct Debit.Post payment
Method initiated by the customer, where authentication and authorization happen after the transaction has been issued.
Examples: Konbini, Boleto Bancário, Multibanco.Local Card Scheme
Local card schemes—specific to certain markets—often operate much like traditional cards, but some schemes will be more sophisticated, for instance offering card and bank transfer options.
Examples: MisterCash (Belgium), Carte Bleue (France), Multibanco (Portugal), Elo (Brazil).Cash
Physical form of currency represented by banknotes and coins that can be exchanged for goods, typically during product delivery.
Channels
The concept of payment method and provider are interconnected in the sense that a given payment method may be available through several providers within the same market, the same way that a given provider may support multiple payment methods. They are also selected by two different entities, the method being chosen by the customer through the Switch Dashboard, and the provider defined by our Dynamic Routing module.
The combination of a payment method and a provider represents a channel in the Switch Platform. It is an actual medium that can be used to perform a financial transaction (e.g. Credit Card through Elavon, or Alipay through Worldpay).
A Switch channel is configured through the Switch Dashboard using the API keys for the merchant account that you have opened with the provider. By setting up multiple channels for the same payment method, and leveraging our Dynamic Routing component, you can define specific rules for real-time transaction routing between multiple providers.
Higher Acceptance Rate
Providers have different acceptance rates, which depend on multiple variables, such as card brand, issuing country/bank, MCC, and amount. Failed transactions result in lost sales and increased customer support costs. Our Platform can retry transactions in real-time across multiple providers to maximize acceptance rates.
Lower Processing Costs
A rise in cross-border transactions is pushing processing costs up, especially due to inter-regional interchange fees and card scheme fees. Switch calculates expected commissions based on multiple processing variables to choose the optimal transaction route.
Transactions
The diversity of the payments ecosystem poses a great challenge to global companies, as each payment channel requires its own specific integration, which is costly to build and maintain. As payment channels start to add up, companies become unable to optimize their payment operations in a timely manner.
With this challenge in mind, we devised a way to abstract every transaction flow in a single one, independent from the payment method, allowing companies to invest one time into integrating with our platform and gain access to the entire value chain without further development investments.
To this effect, we divide a financial transaction into multiple correlated steps, which we either call elements, or lifecycle events. Each of these steps represents a different phase in the transaction lifecycle within the Switch Platform, and therefore, requires and stores different data. Therefore, the concept of transaction within the Switch Platform can apply to every element after the creation of a charge and any element that requires communication with a provider.
Supporting different payment methods under the same platform in a standardized manner brings additional challenges when it comes to transaction execution. Each payment method is designed with its own philosophy when it comes to processing transactions, and therefore requires different steps, and different execution flows.
Accommodating this diversity under the same platform required us to support four transaction flows.
| Transaction Flow | Payment executed automatically? | Recurring payment? |
|---|---|---|
| 1. Capture on Creation | Yes | No |
| 2. Auth-Capture | No | No |
| 3. Recurring on Auth | Yes | Yes |
| 4. Recurring on Capture | No | Yes |
Capture on Creation
This flow targets transactions that only need to take place once, and where the funds do not need to be captured at a later time, therefore not requiring an authorization to take place.
From a Switch Platform perspective, this flow does not require you to create the payment element to execute the funds transfer. The Processing Application will automatically create the payment element once you create the instrument, given that the funds will be captured right away.
Recurring on Auth
Destined for payments that need to happen on a frequent basis, this flow allows you to create a reusable instrument element that can be leveraged to make multiple payments.
This particular recurring flow automatically executes the payment element when the instrument is created. It means that for the first payment, you only need to create the instrument, as the Switch Platform will automatically create the first payment. For subsequent transactions you only need to create the payment element, referencing the same specific instrument.
Auth-Capture
An Auth-Capture flow is intended for transactions that take place once, and have the funds captured at a later time, thus requiring two steps: Authorization and Funds Capture.
The Authorization is executed when the instrument element is created in our platform, either automatically using our Dynamic Forms or manually leveraging our REST API. At this stage the money has been reserved from the customer accounting platform but has not yet been transferred. The actual funds transfer only happens when the payment element is created in the Switch Platform.
Recurring on Capture
Designed for transactions that need to take place regularly, enables you to create a reusable instrument element that can be used to perform multiple payments.
This particular recurring flow does not automatically execute the payment element when the instrument is created. In short, it requires you to create a payment element every time you want to execute a transaction.
Elements
With the current and future variety of payment methods, ensuring they can conform to standardized operation is paramount. To be truly effective, the utilization experience of a payments platform should not require different integrations or execution flows.
Our platform defined elements to this effect, to allow a global way of handling payments in a single integration. By utilizing the elements described below we ensure our platform is future-proof, by handling any current and future payment methods in a uniform manner.
- 1
CHARGE
Signals the merchant’s intent to do a fund transfer. It is at this stage that the payment method and provider are selected as configured.
- 2
INSTRUMENT
Element providing the information required to authorize one or more transactions for the target payment method (e.g. credit card details).
- 3
PAYMENT
Stage where transaction captures actually take place. May be initiated by Switch for certain transaction flows.
- 4
REVERSAL
Reversals serve two purposes. They are used for reversing a capture or refund that has not yet been cleared, or for voiding an authorization.
- 5
REFUND
Allows the complete or partial return of the funds to the originating customer. Can only be done for successful transactions and is initiated by the merchant.
- 6
DISPUTE
Initiated by the provider, this element represents a customer or issuing bank questioning the validity of the original transaction and may result in funds’ reversibility if the claim is successful.
Lifecycle Events
Learn more about lifecycle events.
Lifecycle events are the best way to keep track of transactions' statuses on the server-side, and update your databases and systems accordingly.
The Switch Platform relies on a microservices' architecture to provide platform components besides the actual transaction processing. In order to achieve this, it uses an event-driven philosophy for cooperation and routing between services.
One added benefit of doing so is that it allows you to subscribe to notifications regarding the lifecycle of transactions. Examples of such notifications would include events like charge.created, instrument.authorized, or payment.success. These can be leveraged to orchestrate payment-related activities on your side.
Security
It takes a lot of effort to make sure payments are secure. Fraud can be costly for merchants and financial institutions, so it is important to ensure all types of threats, attacks, and suspicious activity is closely monitored. At Switch, we have six main security principles we follow when it comes to making sure your transactions are safe.
Secure network and systems
Software updates, firewalls, monitoring, logging.
Safety of cardholder data
Hashing, encryption, restricted access to servers, storage, and networks.
Vulnerability management program
Intrusion Detection System (IDS), File Integrity Monitoring (FIM), monitoring and logging.
Access control
Restrict users access, track users access, restrict physical access.
Monitoring and testing practices
File Integrity Monitoring (FIM), internal and external scans, incident response plan.
Information security policy
Clear processes and policies communicated to all staff who work at Switch.
PCI DSS and PCI PIN
Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards formed in 2004 by Visa, MasterCard, Discover Financial Services, JCB International, and American Express that aims to secure credit and debit card data transactions against data theft and fraud. The PCI Security Standards Council defines a set of requirements intended to ensure that all companies that process, store, or transmit credit card information maintain a secure environment.
Level 1
On-site assessment conducted yearly by a Qualified Security Assessor.
Level 2
Quarterly internal and external scans performed by an Approved Scanning Vendor.
Level 3
Yearly internal penetration tests by an Approved Scanning Vendor.
Level 4
Yearly revision of security and quality procedures.
In short, PCI DSS is a set of regulations that apply to all entities that store, process, and/or transmit cardholder data. It covers technical and operational practices for system components included in or connected to environments with cardholder data. If you accept or process payment cards, PCI DSS applies to you. The criteria for Level 1 PCI DSS compliance depends on which card brands the merchant accepts, as follows:
- Visa, Mastercard, and Discover define Level 1 merchants as those processing more than 6 million credit card transactions annually;
- American Express’s minimum for Level 1 is 2.5 million transactions per year;
- JCB’s Level 1 starts at 1 million credit card transactions per year.
Switch is PCI DSS Level 1 compliant. But what does that mean exactly? And why should you care about it?
PCI DSS is a challenging, complex, and considerably expensive certification to achieve. By integrating with Switch you save your business the effort of going through with it.
To meet PCI DSS Level 1 Standard there are five main required processes, which every compliant company like Switch must go through every year.
- Annual Report on Compliance (ROC) by a Qualified Security Assessor (QSA) or Internal Security Assessor;
- Quarterly network scan by Approved Scan Vendor (ASV);
- Penetration test;
- Internal Scan;
- Submission of completed Attestation of Compliance form.
Around 250 requirements comprise the Payment Card Industry (PCI) Data Security Standard. You can find a simplified version of the requirements necessary to meet the PCI Compliance Security Standard Council’s goals in the table below.
| Goals | PCI DSS Requirements |
|---|---|
| Build and Maintain a Secure Network | 1. Install and maintain a firewall configuration to protect cardholder data 2. Do not use vendor-supplied defaults for system passwords and other security parameters |
| Protect Cardholder Data | 3. Protect stored cardholder data 4. Encrypt transmission of cardholder data across open, public networks |
| Maintain a Vulnerability Management Program | 5. Use and regularly update anti-virus software or programs 6. Develop and maintain secure systems and applications |
| Implement Strong Access Control Measures | 7. Restrict access to cardholder data by business need-to-know 8. Assign a unique ID to each person with computer access 9. Restrict physical access to cardholder data |
| Regularly Monitor and Test Networks | 10. Track and monitor all access to network resources and cardholder data 11. Regularly test security systems and processes |
| Maintain an Information Security Policy | 12. Maintain a policy that addresses information security for employees and contractors |
TLS and HTTPS
The Hypertext Transfer Protocol (HTTP) is the basic communication protocol that both clients and servers must implement in order to be able to communicate. It transfers information between the browser and the server in clear text, allowing the network, through which the information passes, to see the information transmitted. HTTP Secure (HTTPS) was introduced to allow the client and the server to first establish an encrypted communication channel, and then pass the clear text HTTP messages through it.
It is crucial for payment security that merchants implement SSL protocol on their websites. Transport Layer Security (TLS), and its now-deprecated predecessor, Secure Sockets Layer (SSL) allows for the encryption of the information that goes through the website, such as the payment card details that customers share during the checkout process.
HTTPS TLS provides three important security measures.
- Confidentiality. It protects communication between two parties from others within a public medium such as the internet.
- Integrity. It ensures information reaches its destined party in full and unaltered.
- Authentication. It grants that the website is actually what it claims to be by also checking its legal identity.
Two Factor-Authentication
Two-factor authentication is an extra layer of security designed to ensure that only the rightful users can access their respective accounts on the Switch Platform, namely by logging into the Switch Dashboard.
Two-Factor Authentication is enabled under settings for every user with access to the Dashboard.
API Keys
Looking for more details on the Switch Dashboard?
The Switch Dashboard offers a comprehensive and user-friendly interface to support your payment strategy. Check out our Dashboard features.
Different combinations between the Merchant API Keys or Processing API Keys and your account ID grant authentication in your requests. It is important to be well aware of when to use each of the keys and how to gain access to them. If you have any trouble with these, please contact our Support Team.
- Public Key. Used in requests coming from the client-side, to create dynamic forms and instruments.
- Account ID and Private Key. Used in requests coming from the merchant server, to create charges, payments, reversals, and refunds, as well as accessing management APIs. This key SHOULD NEVER BE SHARED in client-side code.
Fraud Prevention
For every transaction, there are multiple security steps that can be taken. These can be either automatically applied by Switch or are optional and can be enabled through our applications.
Tokenization
Want to know more about the Switch Vault?
Learn more about how we use tokenization to facilitate payments.
Tokenization helps to authenticate the customer during the purchase without affecting the security of a transaction. The process uses tokens which are random strings of characters that replace sensitive information, namely credit card numbers. Tokenization reduces the chances of a data breach because if a token is stolen, it has no use for fraudsters.
The Switch Vault allows for the tokenization of any Switch parameter. This means our application is not limited to card details but can go as far as being used to create instruments for different payment methods without the need for further input. The Vault Application grants:
- PCI DSS-compliant transaction initiation using the same payment credentials in multiple providers;
- Multi-channel use of the same payment instrument (e.g. in-store capture, online refund);
- GDPR-compliant means of storing customer data for authentication (e.g. name, email, address, social security number).
3D Secure
Looking for more information on Risk management?
Learn more about how you can apply our Risk rules to your fraud prevention strategies.
3D Secure authentication is an additional security layer for card-not-present transactions. The name comes from Three Domain Secure, which is a messaging protocol that involves three domains, such as a bank, the technology that processes the transaction, and the issuing bank.
The system usually requests tokens or biometrics to authenticate cardholder information, which can decrease the number of fraudulent attempts. Additionally, by using 3DS the liability on every transaction that is successfully verified is shifted from a merchant to the issuing bank. You can enable 3D Secure Authentication using our Risk Application.
Switch Risk Application
The Risk Application exists to keep your transactions safe through straightforward methods that can be easily automated.
Risk is present in your transactions from the very start and it defines the ways in which these transactions are processed and settled. The goal of this application is not only to offer constant vigilance over your payment operation, but also aid you in understanding what went wrong and how it can be addressed. Risk rules are designed to trigger the following actions:
- Allow: Allow the creation of the flagged object;
- Block: Block the creation of the flagged object;
- Review: Set the creation of an object up for review;
- Enable 3DS: Enable request for 3D Secure authentication.
Stability and Scalability
At Switch, we understand that stability and scalability are big concerns for the businesses that work with us. There are multiple efforts we make towards ensuring our services and application are reliable.
| Goals | Procedures | |
|---|---|---|
| Systems resilience High-Availability Stability | - 24/7 alerting and monitoring: All infrastructure is monitored about system telemetry. - Application monitoring: all apps communicate to a logging system that centralizes infrastructure logs. - Monitoring of replica databases. - Critical failures are communicated through SMS/email, both internally and to our customers. | |
| High Availability SLAs | - Historically, our system's availability surpasses 99.9%. - We are deployed in multiple cloud services and DNSs. | |
| Automatic Backup Disaster Recovery | - Daily database backups. - Multiple and geographically dispersed database locations - Automatic disaster recovery: server provisioning, backup import, build, and run app services. - How fast? We annually test all disaster recovery procedures and it takes on average 2h. | |
| Zero Downtime Updates | - Use of load balancers to route requests to machines running upgraded versions. - Use of load balancers to rollback requests to machines running previous versions. | |
| Scalability | - Full horizontal scalability. - Switch has a microservices architecture, based on Docker containerization. - Databases and applications run in different and multiple machines. - Script for automatic microservices instances deployment. - Service discovery: infrastructure orchestration system to which applications communicate to find the right servers. | |
| Big Data Infrastructure | - Data warehousing: different data representations to optimize data queries. - Data denormalization. - Event sourcing. - Stream processing: event-based database to be consumed by different applications. - Transaction flow for client-side tokenization. - Fully PCI Level I compliant: servers, data, network, and employees have implemented security measures to guarantee bank-grade security. - GDPR compliant: Switch is considered a processor, so personal data privacy is fully encrypted and managed by a data controller, so it can be deleted on request. |
Next Steps
Head over to Integrating with Switch to learn the integration patterns available and choose the one that best suits your needs.